WannaCry Ransomware Attack: All there is to know
Ransomware
It’s a cyber security buzzword that you’re likely to be aware of, thanks to the huge cyber attack over the weekend that hit over 150 countries. Ransomware is a type of virus that encrypts a computer, network or files and demands money in return for the files to be decrypted.
Who was hit by WannaCry Ransomware?
‘WannaCry’, ransomware is the name of the computer malware which caused firms to grind to a halt globally – hitting the headlines for infecting many computer systems of NHS Hospitals in the UK.
NHS England declares attack as ‘Major Incident’
News broke at 15:30 on Friday afternoon, with a reported 16 NHS organisations initially affected. This number rose to 25 by 17:30, with news breaking that NHS organisations in Scotland were also under attack. Figures finally rose to 45 by Saturday morning. The cyber attack has resulted in many patients being turned away from affected hospitals and diverted elsewhere until systems are back up and running.
How does WannaCry work?
This particular attack works by disabling victims files’, with attackers demanding $300 (£230) to restore them. So far, only $50,000 (£39,000) has been paid, but WannaCry warns that if payment is not made, the ‘ransom’ increases to double after three days and threatens to delete files if payment is not made within seven days.
Victims infected with the latest WannaCrypt ransomware are instructed to pay for “Wanna Decryptor”. This updated application is needed in order to retrieve encrypted files, but only at a cost of 0.1 Bitcoins (approximately $300). The latest version of the “Wanna Decryptor” is even more super-charged than the original variant, making it so robust that it destroys anti-malware software that attempts to interfere with the process.
Microsoft has said that the exploit code used by WannaCrypt is designed to target unpatched Windows 7 and Windows Server 2008, or even earlier systems such as Windows XP.
How do I avoid being hit by ransomware?
The UK National Cyber Security Centre – the firm tasked with keeping the nations’ critical infrastructure safe from cyber attacks – have published guidelines to advise firms on how to stay protected.
The NCSC advises that large organisations should;
- Ensure that software patches are up to date.
- Ensure reliable antivirus software services are in place, up to date, and are conducting regular scans.
- Ensure all outgoing and incoming emails are scanned for malicious attachments.
- Educate employees on identifying scams, malicious links and suspicious emails that could potentially contain viruses.
- Companies should back up their critical data.
NCSC advises small businesses and individuals should;
- Run Windows Update
- Ensure antivirus software is in place, up to date and running frequent scans.
- Ensure all important data is backed up, just in case it is held at ransom.
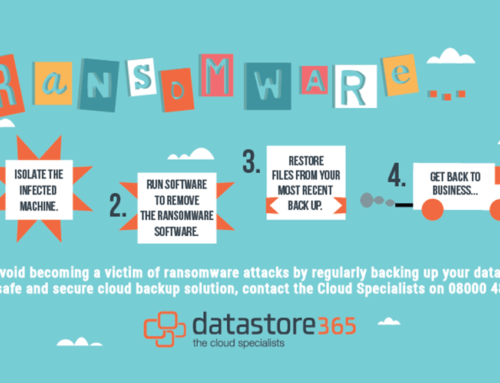
What if I’ve already been hit by a ransomware attack?
-
- Do not pay the ransom. There is no proven evidence that attacks are releasing encrypted data.
- Contact the law enforcement and provide as much information on the attack as possible.
- Restore data backups.





Leave A Comment
You must be logged in to post a comment.