Bristol Church becomes latest victim of ransomware attack

A group of churches in Bristol have become the latest victims of a ransomware attack.
A group of churches in Bristol have become the latest victims of a ransomware attack, after an employee opened a suspicious email containing a malicious attachment.
The group, made up of 46 churches, within the Bristol and South Gloucestershire Methodist Circuit, unfortunately, fell victim to the cyber attack, resulting in the loss of an entire database of financial records.
An employee listed an advert for a job position, when a reply email arrived with the subject line: “Job application – please see attached CV.”.
Once the attachment was opened, every document on her computer instantly turned to a scrambled mess, and the hackers then sent a demand for money in return for the corrupt files.
The church has refused to pay the cyber criminals, and has given all details to the police to warn other people of what to look out for to prevent future cyber attacks from happening.
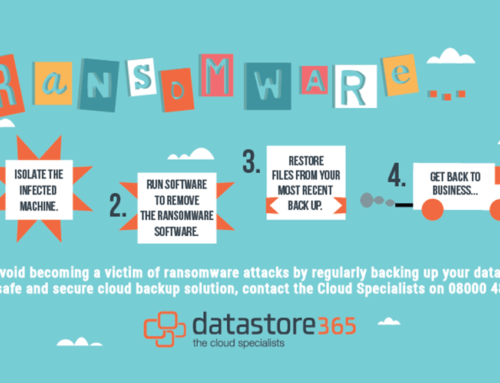
The church’s IT system was infected with ransomware – a type of malicious software that allows cyber attackers to take control of a computer, blocking access to the legitimate users until the ransom is paid. In this instance, the church group lost six years of documents that cannot be retrieved.
To prevent a cyber attack from corrupting your businesses critical data, authorities urge businesses to regularly backup data, meaning all documents can be instantly retrieved, allowing firms to return to business as usual.
Most importantly, to learn more about our safe and secure cloud solutions that can protect your business from harm, give the Cloud Specialists a call on 08000 481 848.





Leave A Comment
You must be logged in to post a comment.